2020
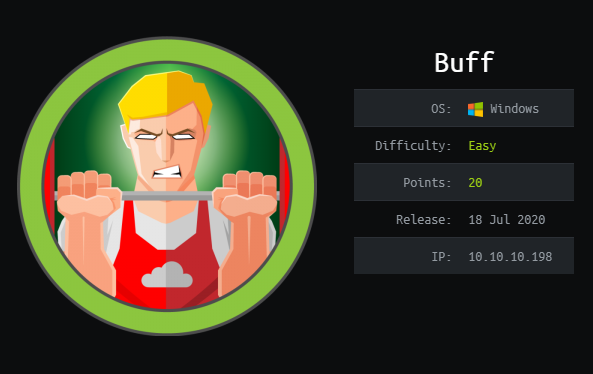
HTB: Buff
HTB: SneakyMailer
HTB: Tabby
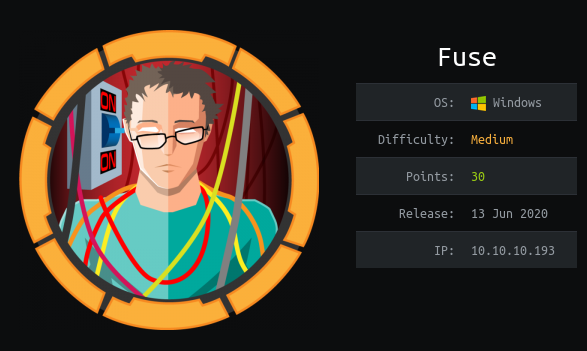
HTB: Fuse
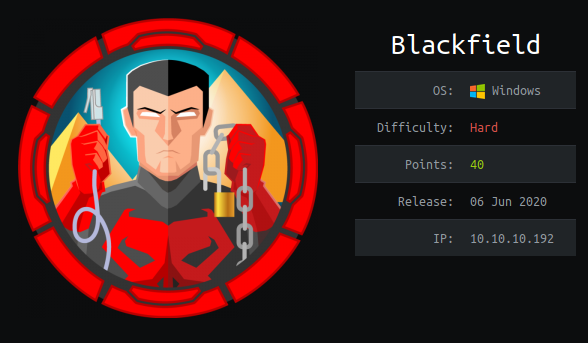
HTB: Blackfield
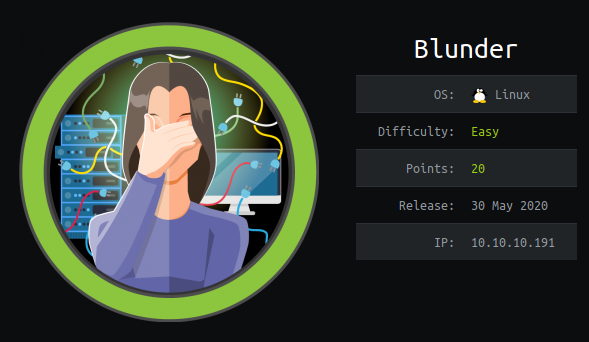
HTB: Blunder
HTB: Travel
HTB: Cache
HTB: Admirer
HTB: Quick
PoseidonCTF: The Large Cherries
The Large Cherries
rgbCTF: Too Slow
I’ve made this flag decryptor! It’s super secure, but it runs a little slow.
rgbCTF: Name a more iconic band
I’ll wait.
rgbCTF: icanhaz
can u haz a meaningful career in cybersecurity tool development? we hope so!
rgbCTF: Hallo?
The flag is exactly as decoded. No curly brackets.
rgbCTF: Vaporwave2
I got two versions. I got twooo versions…
redpwnCTF: static-pastebin
I wanted to make a website to store bits of text, but I don’t have any experience with web development. However, I realized that I don’t need any! If you experience any issues, make a paste and send it here
redpwnCTF: CaaSiNO
Who needs regex for sanitization when we have VMs?!?!
NahamCTF: Trapped
Help! I’m trapped!
NahamCTF: Time Keeper
There is some interesting stuff on this website. Or at least, I thought there was…
NahamCTF: Simple App
Here’s a simple Android app. Can you get the flag?
NahamCTF: Rotten
Ick, this salad doesn’t taste too good!
Nahamctf Readtherules
Read The Rules
NahamCTF: Microsooft
We have to use Microsoft Word at the office!? Oof…
NahamCTF: Lucky
Oooh, an encrypted filesystem, lucky you!
NahamCTF: Localghost
BooOooOooOOoo! This spooOoOooky client-side cooOoOode sure is scary! What spoOoOoOoky secrets does he have in stooOoOoOore??
NahamCTF: Glimpse
There’s not a lot to work with on this server. But there is something…
NahamCTF: Finsta
This time we have a username. Can you track down NahamConTron?
NahamCTF: Fake File
Wait… where is the flag?
NahamCTF: Extraterrestrial
Have you seen any aliens lately? Let us know!
NahamCTF: Dangerous
Hey! Listen!
NahamCTF: Candroid
I think I can, I think I can!
NahamCTF: Awkward
No output..? Awk-o-taco.
NahamCTF: Alkatraz
We are so restricted here in Alkatraz. Can you help us break out?
DefenitCTF: MoM’s Touch
We’re given a binary called momsTouch for this challenge. When we run this binary, we get the following message:
HackPack: Super Secret Vault
Downloading the index.php file for this challenge, we see the following code:
HackPack: Hacking USSR
We first need to log into the machine with ssh:
HackPack: Treasure
Visiting https://treasure-map.cha.hackpack.club/robots.txt we can see the following:
HackPack: SSME
Connecting to the vulnerable message encryption service returns a small User Interface:
HackPack: Quote of the Day
We are given a client to connect to cha.hackpack.club:41709. Loading the client up gives us a simple user interface to work with:
HackPack: Paster
Visiting https://paster.cha.hackpack.club gives us a text box to enter input into. All input is truncated, and returned to the screen, giving us a pretty good idea that this’ll be a XSS vulnerability. Trying a variable of difficult payloads (<script src=, <iframe src=,
HackPack: jsclean
We’re given a python script as reference, and an address to connect to:
HackPack: Humpty
We first need to connect to the machine with ssh:
HackPack: Custom UI
Visiting https://custom-ui.cha.hackpack.club gives us a user interface, where we can enter RGB values for a button, along with its text. Catching the request and setting “xdata=’” in the POST request gives us the following error:
Hackpack - Birthday
Visiting https://online-birthday-party.cha.hackpack.club/account.php and signing up for a new account takes us to a page where we can see what other users share our birthday.